Android permissions and their meaning
Related Videos: App permissions: What you need to know (May 2024).
The permissions of Android apps are sometimes of great importance, but are still neglected. You can usually tell from them whether an app is legitimate or whether it should act as disguised spy software on your smartphone. Finally, apps with the appropriate permissions can access large parts of your data. In these practical tips, we will show you how to protect yourself against attacks and what the individual rights mean.
Where can I check an app's permissions?
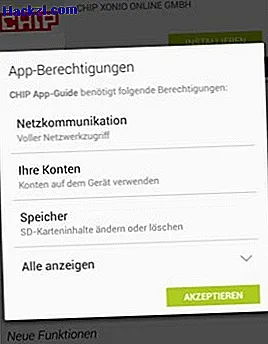
- It's quite simple: If you install an Android app - whether directly on the device or from the PC - you will first see the list of permissions. The app will not be installed until you have confirmed this with "Accept".
- In the browser version of the Play Store, it is particularly convenient to access permissions. Simply click to the right of "Overview", "Testimonials" and "New Features" on the "Permissions" tab.
- Alternatively, you can also use the free app "APEFS", which informs you about the rights of the currently installed apps.
Critical and safe permissions
In order to differentiate between critical and harmless permissions, Google arranged them according to certain criteria when downloading the app: Potentially questionable permissions appear at the top of the list, all others only after clicking on "Show all" (see screenshot above). There are a total of around 160 permissions that an Android app can request. However, the largest part is unproblematic and does not pose a threat to your data.
Below is a selection of the most important and common permissions for Android, along with a brief description and assessment.
Find known accounts
The app can see which accounts your smartphone is already connected to. This is useful, for example, if the app is to connect to Facebook.
Take pictures and videos
The application always has full access to your cameras in the cell phone. If the app has nothing to do with images, this permission is to be viewed rather critically.
Unrestricted internet access
This is particularly dangerous in connection with other notifications, since the app can upload spied data into the Internet in an uncontrolled manner. Caution should be exercised here, particularly with dubious apps.
Control vibration alarm
The authorization only means that the app can access the Vibartions engine in the smartphone - for example, to vibrate when notifications are received. A data theft is hardly to be feared here.
Exact (GPS) location
This authorization enables the app to determine your current location very precisely. This is indispensable for card services, for example, but must be viewed critically with many other apps.
Get network connections
The app can only ask which network you are on - for example 3G or WLAN. This is used, for example, so that an app only downloads larger downloadable content via WLAN and not via the mobile data connection.
Deactivate hibernation
This is used, for example, by video players so that the display remains switched on during playback. The authorization can lead to an increased battery consumption and is therefore harmless.
Read calendar appointments and confidential information.
This authorization gives the app access to all of your calendar data and should therefore be checked very carefully.
Install Packages
The app can install other apps itself. The authorization should only be available for market applications such as the "Amazon App Store".
Read confidential log data
This authorization should only be used with caution - especially for apps from third-party developers. The log data sometimes contains very sensitive information and should only be used for detailed error reports.
Call phone numbers directly
This entails the risk that apps call chargeable numbers and thus cause greater financial damage. For apps that have to do with phone calls, such as "Skype", the authorization is rather harmless.
Change or delete USB memory contents
This authorization is required by many apps to transfer data such as saves to the memory. At the same time, they also have access to private data stored on the storage. With dubious apps you should be very careful here.
$config[ads_text5] not foundRead and identify phone status
This access is not without problems because the IMEI and IMSI numbers of the cell phone can be queried. The authorization is still used by many apps so that they can pause independently on incoming calls.
End background processes
For example, task managers need this right so that they can function at all. In the worst case, it can lead to data loss, but not to data theft.
Record audio
Sometimes used by applications when they respond to acoustic signals, such as a tuner. Otherwise the authorization should not be found, even if the possible data yield can hardly be used.
Send short messages
This authorization can be misused, for example, by an app signing up for an expensive subscription without you noticing. It should therefore also be used with caution.
$config[ads_text6] not foundConclusion
Take the permissions seriously and check whether they are really needed by the app before installation. Look for more information about the app or the permissions that make you suspicious and, if in doubt, prefer not to download it. You should stay away from dubious apps in particular - for example with a poorly translated description and rather negative reviews. You can find detailed reviews of numerous Android and iOS apps by the way in our "App Area".
